- /
- /
- /
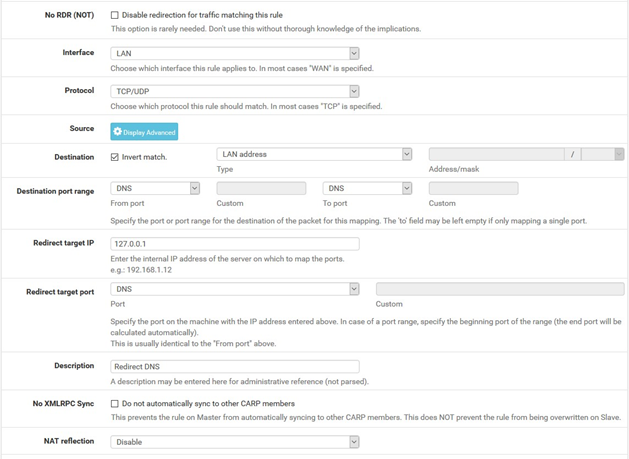
Redirecting Client DNS Requests
To restrict client DNS to only the DNS Resolver or Forwarder on AZTCO-FW software, use a port forward to capture all DNS requests clients send to other servers.
Note: Either The DNS Forwarder or DNS Resolver must be active and it must bind to and answer queries on Localhost, or All interfaces.
The following example uses the LAN interface, but the same technique will work with any local interface.
- Navigate to Firewall > NAT, Port Forward tab
- Click
Add to create a new rule
- Fill in the following fields on the port forward rule:
- Interface: LAN
- Protocol: TCP/UDP
- Destination: Invert Match checked, LAN Address
- Destination Port Range: DNS (53)
- Redirect Target IP: 127.0.0.1
- Redirect Target Port: DNS (53)
- Description: Redirect DNS
- Click
- NAT Reflection: Disable
When complete, the port forward must appear as follows:
Note: If DNS requests to other DNS servers are blocked, such as by following Blocking External Client DNS Queries, ensure the rule to pass DNS to 127.0.0.1 is above any rule that blocks DNS.
With this port forward in place, DNS requests from clients made to any external IP address will result in the query being answered by the firewall itself. Access to other DNS servers on port 53 is impossible.
Tip: This can be adapted to allow access to only a specific set of DNS servers by changing the Destination network from “LAN Address” to an alias containing the allowed DNS servers. The Invert match box should remain checked.
| Warning: Clients using DNS over TLS or DNS over HTTPS could circumvent this protection. See Blocking External Client DNS Queries for details. |
